Regional coverage across NY Metro and northern New Jersey
VMS supports businesses across NYC, Long Island, Westchester, and northern New Jersey, with broader infrastructure support available for larger projects.
Proactive support, practical security, camera systems, and cloud communications for small and medium businesses across the NY metro area and northern New Jersey. Custom AI applications and private hosting are available for teams that need secure automation, while enterprise services remain available for NOMAD data centers and HPC procurement.
For small and medium businesses across NYC, Long Island, Westchester, and northern NJ that need stable systems, tight security, and a partner who owns the outcome.
Day-to-day support, onboarding, and vendor coordination for NY Metro SMB teams.
Security-first operations that reduce risk without slowing down your staff.
Microsoft 365, email security, and cloud PBX systems managed end-to-end.
Commercial surveillance design and Ubiquiti Protect deployments for offices, retail, warehouses, and multi-site operations.
Growing businesses usually want the same things from an IT partner: clear accountability, regional coverage, practical support, and a credible path from day-to-day operations into more complex infrastructure work.
VMS supports businesses across NYC, Long Island, Westchester, and northern New Jersey, with broader infrastructure support available for larger projects.
Support stays cleaner when endpoint issues, camera access, Microsoft 365, networking, and site operations are handled under one operating model.
The engagement model is rooted in practical support, lifecycle planning, and disciplined rollout work instead of one-off installs that leave ownership unclear.
Clients can start with managed IT today and expand into private AI hosting, HPC sourcing, or modular capacity planning when the use case is real.
Most clients call VMS when they have outgrown ad hoc support, security is inconsistent, or site systems like phones, Wi-Fi, and surveillance are being managed by too many separate vendors.
Law firms, finance teams, healthcare groups, and service businesses that need dependable support, better identity controls, and cleaner vendor accountability.
Organizations juggling storefronts, branch locations, phones, Wi-Fi, cameras, and staff turnover that cannot afford a reactive support model.
Teams that rely on stable connectivity, camera coverage, mobile devices, and practical escalation support across offices, yards, and receiving areas.
Most engagements begin with one practical priority: stabilizing support, improving site visibility, or scoping a secure infrastructure project without overbuying.
Common starting point: recurring tickets, unclear escalation paths, inconsistent MFA and backup hygiene, and too many vendors touching the environment.
Typical need: better entrances, receiving areas, parking, and after-hours visibility without creating a disconnected surveillance stack.
The right entry point is usually an internal knowledge or workflow use case with clear retention, access, and hosting boundaries.
NYC Access-A-Ride provider
VMS has supported Professional Transit for more than 20 years, handling IT systems and security equipment as the company expanded to a third location.
The first project is rarely just a helpdesk problem. It is usually a combination of support gaps, security drift, vendor sprawl, and systems that no longer fit how the business operates.
Most SMBs reach out when support, security, phones, Wi-Fi, and cameras are spread across too many vendors. We bring those systems back under one accountable operating model.
The goal is not extra tools for their own sake. It is better identity controls, cleaner patching, reliable backups, and faster incident response that still fits how the business actually works.
The best engagements start with immediate issues, then move into lifecycle planning, cloud operations, camera systems, and private AI workflows that can be managed long term.
We design camera systems for offices, retail locations, warehouses, entrances, and perimeter areas across New York and northern New Jersey. That includes Ubiquiti Protect camera planning, recorder sizing, retention strategy, and remote access that fits into the same managed IT operating model.
Interior, exterior, dock, lobby, and parking-area coverage using camera placements that reflect real workflows instead of generic package counts.
Recorder sizing, retention targets, mobile review access, and operational ownership so footage is actually useful when you need it.
Camera systems touch PoE switching, VLANs, Wi-Fi, remote access, user permissions, and mobile devices. We support them as infrastructure, not a disconnected install.

A compact indoor dome for lobbies, offices, hallways, and reception areas where you want low-profile hardware and clean day-to-day coverage.

A stronger exterior camera with AI event detections for parking lots, receiving areas, dock doors, yards, and other longer-sight-line views.
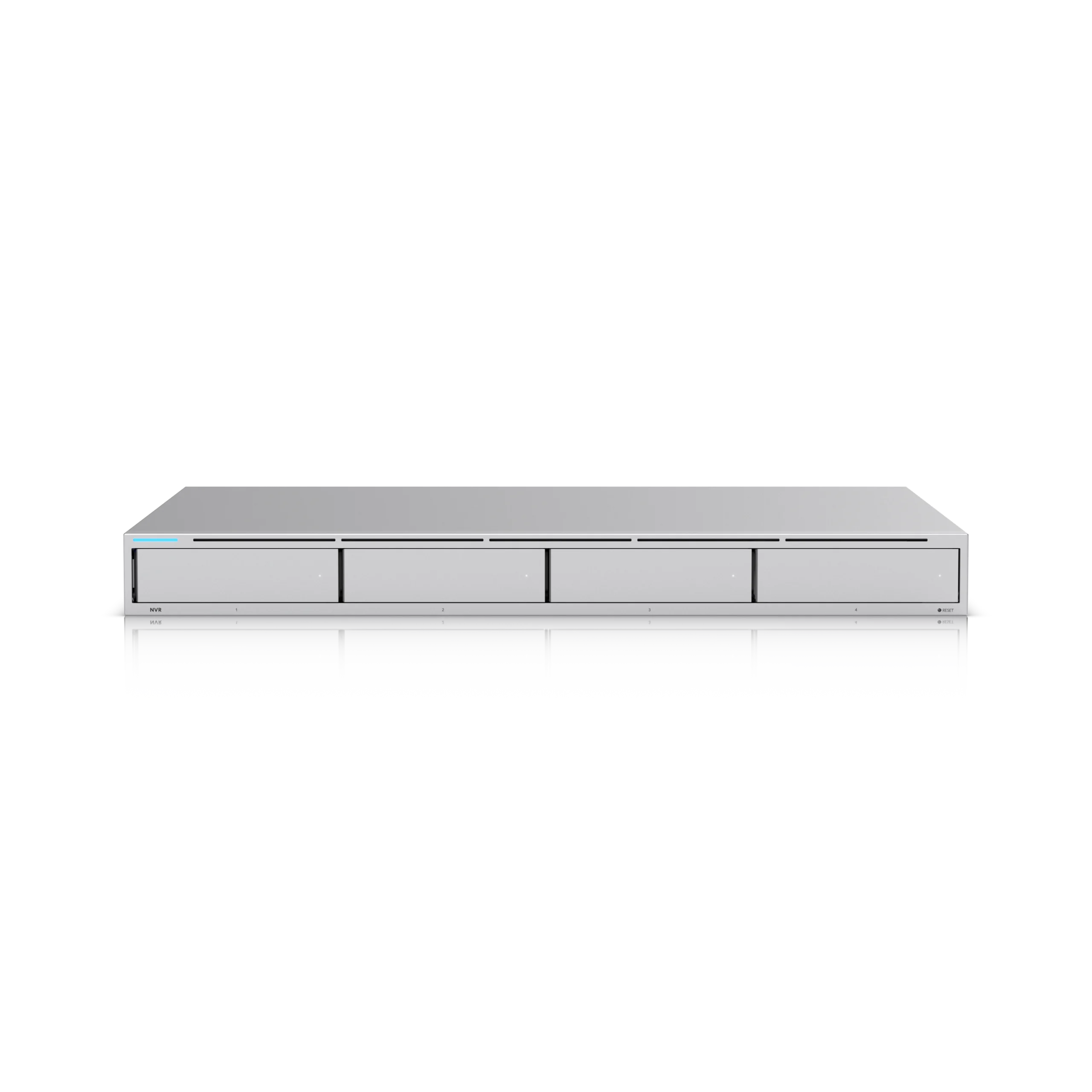
A multi-drive recorder for sites that need predictable evidence retention, cleaner user access, and a supportable UniFi Protect review workflow.
We design, build, and operate AI systems that integrate with your environment and keep sensitive data under your control.
Purpose-built copilots and automations designed around your workflows, data boundaries, and security posture.
Dedicated infrastructure for organizations that want AI capability without putting sensitive data into shared environments.
NOMAD modular data centers, HPC server inventory, and deployment support for teams that need more compute without losing operational control.
Modular 2MW platform with immersion cooling for high-density GPU workloads.
New and used Dell, Supermicro, and HPE systems with NVIDIA and AMD options.
Rack integration, burn-in plans, and delivery coordination into production.
Practical articles on managed IT, cybersecurity, private AI, enterprise infrastructure, and operational reliability.
Explore how custom AI applications can streamline business operations and enhance decision-making for IT decision-makers.
Explore practical cybersecurity strategies tailored for small businesses in the NY metro area to safeguard against threats.
Discover practical IT solutions for SMB owners in the NY metro area facing operational challenges.
Tell us what needs attention first. We will help scope the right support path, camera rollout, or private AI planning conversation without forcing you through a generic sales process.
Best for businesses dealing with support sprawl, cybersecurity gaps, or unreliable day-to-day operations.
Best for offices, retail, warehouses, and multi-site businesses planning a new Ubiquiti Protect deployment or cleanup.
Best for teams planning secure AI workflows, private hosting, GPU servers, or modular compute capacity.